Announcing 2.5 - Cairo

Aug 1, 2012
First off, our apologies for not releasing this version in June, but it is due to the quantity and quality of change it ships with hence more time was required on the quality assurance end. Its in this regard 2.5 is being released in August and so the other versions shift respectively. Well, there has been lots of activity in the Ushahidi kitchen for the last one and a half months. Knives have been sharpened, pots cleaned, ingredients mixed and finally the new release is ready. Ushahidi platform and Crowdmap have both been updated with the new 2.5 code. This release is characterized with some major changes:
Mapping
The mapping code for the main page has been refactored and is no longer tied to the timeline. This means faster load times for your maps. We've consolidated the mapping code into a single JavaScript library; ushahidi.js. This library has an event system which is extensible. The stock events can be triggered for actions such as zoom changes, resizing the map viewport, change of base layer etc. As a by the way, decoupling the timeline from the map effectively means that you can plug in your own timeline. The stock timeline is uses jqplot. This change affects those plugins that hook into the main map such the fullscreen map plugin.
Security changes
The following security issues were identified and fixed in 2.5. On July 1st, members of the Open Web Application Security Project (OWASP) - Portland group and few of our team held an event to drill into the code. Here is a summary of those items we fixed.:
Multiple SQL injections (Timothy D. Morgan, Kees Cook, postmodern)
Missing authentication on comments, reports, email API calls (Kees Cook, Dennison Williams)
Admin user hijacking through the installer (Wil Clouser)
Stored XSS on member profile pages (Amy K. Farrell)
User data exposed in comment API
These important security fixes are included in version 2.5. We have also made them available as stand-alone patch on our security site. Please update your deployments to ensure the most secure version is used. (Crowdmap has been updated with the latest version.)
Settings Table
The structure for the settings table has been modified so that data are stored as key/value pairs. Previously, this table only had one row and each setting was a column. In the new structure, there are only 3 columns: id, key, value. The settings model class (application/models/settings) has the necessary utility methods for retrieving and saving data from/to the restructured table. There is an upgrade script that shall effect this change on your schema.
Permission Tables
User permissions have been refactored into a another table separate table. There is an upgrade script that shall effect this change on your schema. 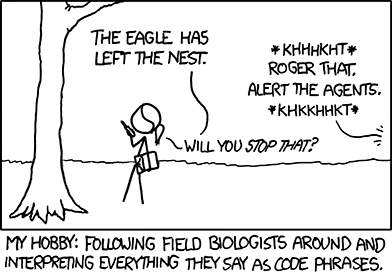
Installer
The installer has been updated to work with the new settings table structure and we now perform the installation check in index.php. Previously, the installation check was being done via a hook (application/hooks/0_init.php)
Configuration Files
The following config files are no longer in the repository: config.php, auth.php and encryption.php. Instead, we are only maintaining their templates (.template.php) which are the ones that the installer uses to create the config files to be used by the application. This change will affect users who automatically update/upgrade their deployment straight from GitHub - a git pull shall DELETE the mentioned config files (the ones we're no longer tracking) so please BACKUP these files before engaging in acts of git fu.
New to Ushahidi?
If you are new to Ushahidi, you can simply click Download and get started. Check out the installation and administration guides on the wiki. Crowdmap is available for those who want to get started without the fuss of a server.
How to upgrade
Upgrading to 2.5 is a staged upgrade. The reason for this staged upgrade is that the changes from 2.4 to 2.5 have many differences. There were changes made on 2.4 hence we have to push out 2.4.1. Deployers on 2.4 will have to upgrade to 2.4.1 first, then upgrade to 2.5. In this case, they will have to manually upgrade to 2.4.1 (e.g. run the upgrade scripts which can be found here i.e ushahidi_2.4_2.4.1.zip), so if they make it to 2.4.1 , they will get a notice to upgrade to 2.5 using the automatic upgrader or manually. If you are on an older version than 2.4, you will need to upgrade from that version to 2.4.1, then proceed with the upgrade to 2.5. We've posted upgrade guidelines by version on the wiki to help you. (And, a wiki page for the more technical folks.)
Upgrade day - Wednesday, August 8th
We want to make upgrade to the latest and most secure version as smooth as possible. To help you get upgraded to the latest version, we will be holding Upgrade office hours on Wednesday, August 8th. You can reach us via skype or IRC. If you can help others upgrade, please sign up for an office hour timeslot.
Appreciation:
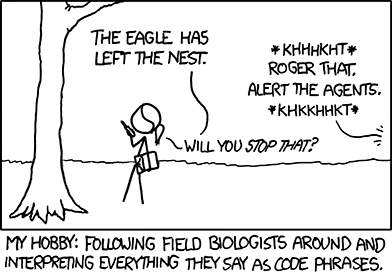
For all the above pieces to be put together, it did not only involve the Ushahidi core developers but the Ushahidi community at large. Special shout outs to Pablo Destefanis, Loren Bell and Anahi Ayala Iaccuci for taking time to give feedback and log issues after testing. Thanks again to OWASP Portland for their security help. A very heartfelt Thank you to Sharon Rutto - currently interning with Ushahidi for the robust tests done on this release. Quality is a key value we aim to uphold. Cartoon image by xkcd licensed under a Creative Commons Attribution 2.5 license. Also, if you are a big XKCD fan, check out Piers Cawley's version of "Major Terrible" as sung at OSCON 2012. (around the 5.30 minute mark). Gold.